Data Breaches:
A data leak may be a catastrophe for many firms. No company wants to face the compromise of private customer data as well as internal corporate information like inventory lists, transaction histories, and other protected data.
Losing customers’ trust can have a disastrous effect on a company’s operations, in addition to the immediate financial effects of fraudulent order placements and bank transfers.
Understanding its causes. What are the leading causes of data breaches in light of this?
A data breach happens when one or more people are permitted to read data they are not authorized to access; as stated in the first article in the series, “What You Need to Know.” take it and frequently alter it. The effects can include database corruption or loss, the disclosure of private information, the theft of intellectual property, and legal obligations to warn and possibly recompense people impacted, depending on the data type involved.
Data Breach Targets:
It becomes a target only when business data is valuable to a third party. Different types of data carry varying degrees of danger for a company and are of varying value to outside parties. The following are some examples of the various sorts of data:
- Individually Recognizable Information includes social security numbers, contact details, dates of birth, academic qualifications, and other particulars.
- Information about money. This includes bank account information, investment information, credit card numbers, expiration dates, and similar data.
- Health-related data. Medical records, prescription medications, therapies, and health issues are also included.
- Inventive property. This comprises blueprints and instruction manuals for products, technical details, mathematical calculations, marketing texts and symbols, proprietary software, and other items the company has created.
- Competition details. This comprises market research, pricing data, competitive information, and business plans.
- Information on the law. This contains records of any legal actions the business may be taking, legal advice on business operations, information on mergers and acquisitions, and regulatory decisions.
- Data on IT security. Measures and network architecture are all included in this.
Third parties who value the data are interested in these forms of information. Information about one’s identity, finances, and health may be sold and utilized for marketing purposes. Intellectual property can be bought, sold, and used to create goods and services comparable to your company’s. Leaked legal information may weaken your legal standing, and competitive information might be sold and exploited by rivals to thwart your ambitions. Because it gives hackers access to all other information on your system, data on IT security is essential in and of itself.
Seven ways that a data breach may occur:
Although there are many different sorts of data breaches, they are virtually always the result of a weakness or gap in security that allows hackers access to the organization’s systems or protocols. Data loss might have disastrous financial repercussions when this occurs. Organizations worldwide suffered losses of $6.9 billion in 2021 due to cybercrime, according to the Federal Bureau of Investigation’s “Internet Crime Report” from that year. Data breaches are mostly to blame for this loss.
Looking at the current state of cyberspace, the following are possible reasons for a data breach:
Accidental data exposure or leakage. Cybercriminals may benefit from configuration errors or mistakes in data judgment.
- Data in motion. Unencrypted data can be intercepted when traveling across a vast area network, through a corporate local area network, or transported to one or more clouds. Organizations can improve their data protection in motion in two ways: uniform cloud security and end-to-end data encryption.
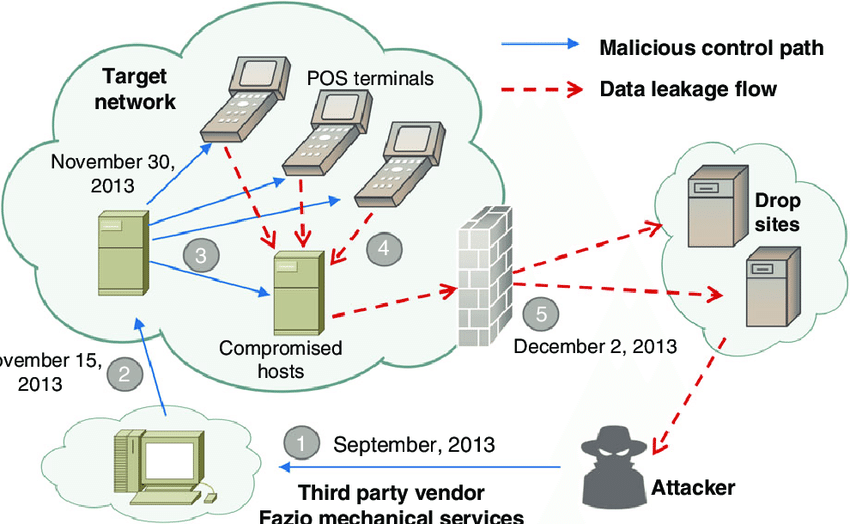
- Gaining access to systems or applications opens the door to malware and malware-related actions, such as SQL injection. Malware, ransomware, or Structured Query Language (SQL).
- Phishing. Phishing can employ other techniques to collect information that can be used to obtain access to data, though it frequently involves malware to steal data.
- DDoS attacks on a large scale (DDoS). Threat actors may use a DDoS attack to divert security administrators so they can utilize other techniques to access data. Additionally, changes made by the company to counter an attack may result in incorrect setups that open up new doors for data theft.
- Keeping a keystroke log. This malicious software keeps track of each keystroke made on a computer and uses that information to steal the usernames and passwords needed to access data.
- Guessing a password. Tools for password cracking can be used to access systems and data when limitless password tries are permitted, or simple passwords are accepted. Password management programs are one approach to help keep passwords organized and centrally secured while assisting users in managing complex passwords.
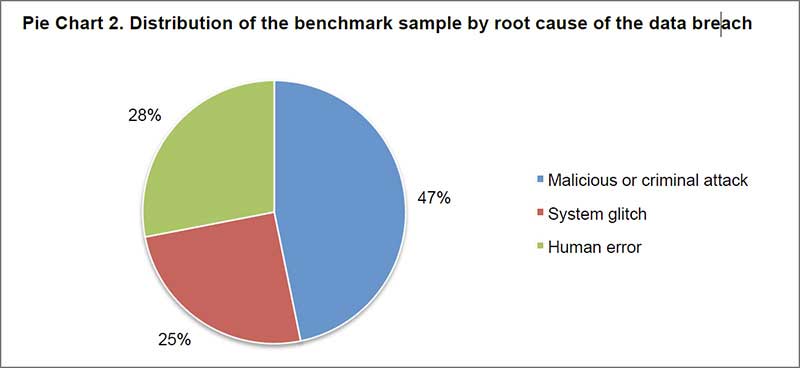
Common Causes Of Data Breaches:
You must be aware of how data breaches happen to be able to protect your personal information as well as the data of your company. We’ll examine the eight most frequent reasons for information breaches. However, there are a few more factors as well.
Too Many Permissions:
Access permissions that are too complicated are a hacker’s dream. Businesses that don’t strictly control who has access to what within their organization will likely have either provided the incorrect permissions to the incorrect people or left outdated permissions lying around for a smug hacker to take advantage of!
Malware:
Malware usage, both direct and indirect, is expanding. By definition, malware is harmful software accidentally placed onto a system, giving a hacker access to take advantage of it and possibly other linked systems.
Simple Fix: Avoid accessing websites that aren’t what they seem to be and opening emails from senders you don’t know because these are common ways for malware to propagate!
Internal Threats:
your enemies close and your friends closer.” What’s to stop the rogue employee, the unhappy contractor, or those who aren’t smart enough to know better from accessing your data and duplicating, modifying, or stealing it?
The simple solutions are to know who you are dealing with, act quickly when an issue appears, and cover everything with the process and procedure supported by training.
Weak Or Stolen Credentials:
Invalid or stolen logins and credentials heavily influence data breaches. Sharing passwords, employing weak or easy-to-guess passwords, and using the same passwords across many devices can all be exploited to cause a data breach.
Social Engineering:
In social engineering techniques like phishing, information is gathered to persuade people to provide particular files or grant access to the attacker. These attacks can grow very sophisticated and imitate legitimate requests in both appearance and tone.
Implement a two-person permission system anytime sharing information or files and teach staff how to recognize phishing attacks. Once more, a US proxy can assist in masking your IP address, preventing hackers from obtaining sufficient data to make their emails more convincing.
Conclusion:
Even though larger organizations with plenty of data are frequently the targets of data breaches, individuals are occasionally targeted. People are frequently the best entrance point for criminal attacks since their security and defenses may be more easily breached. Protecting your data requires using a US proxy in addition to antivirus software and other safeguards.