TECHNOLOGY
How to Create a Smart Folder on a Mac: Step-by-Step Guide
Making folders is a great way to keep all of your Mac items in order. But after a while, having...
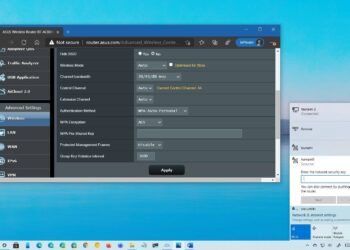
Read moreHow to Change Your Router’s Wi-Fi Password: Step-by-Step Guide
Wi-Fi is the best way to connect different gadgets to the internet. Millions of people use wireless technology on their...
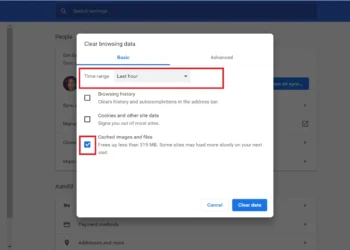
Read moreHow to Clear Your Browser Cache in Chrome, Edge, or Firefox: Quick Guide
While a full computer cache may make it easy to log in and out of favourite sites quickly, a significant...
Read moreHow to See Who Has Unfollowed You on Instagram: Step-by-Step Guide
The main reason you share things on Instagram is to get more people to follow you. Some of your fans...
Read moreHow to Recover Unsaved Word Documents on Windows and Mac: Quick Guide
What if you're working on a Word document and something happens—the power goes out, your laptop battery dies—that stops the...
Read moreHow to Download and Use Clipart:t4h-x66pih4= Turkey: A Comprehensive Guide
The graphic element identified as clipart= turkey serves as a versatile tool in the world of digital design. It represents...
Read moreHow to Use DALL-E 2 to Generate AI Images: Quick Guide
As the number of people who want to make AI pictures grows, many are looking for simple methods, like how...
Read moreHow to search ChatGPT conversations: Quick Guide
People have called ChatGPT a game-changing tool in the tech world. However, its interface does have some limitations. One limitation...
Read moreHow to find your lost phone: Step-by-Step Guide
When you need your phone badly, not knowing where it is can be a real worry. Your smartphone probably knows...
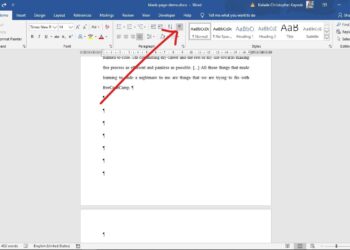
Read moreHow to Delete a Page in Word (Including a Blank Page): Quick Guide
Microsoft Word is one of the best word processors of 2024. Its easy-to-use interface lets you make powerful papers. When...
Read moreRadical © Copyright 2021, All Rights Reserved